Ethical Hacking: The Ultimate Beginner's Guide 2024
Ethical hacking is the practice of locating vulnerable computer systems...
Latest updates, tutorials, and deep-dives from the world of Ethical Hacking.

Ethical hacking is the practice of locating vulnerable computer systems...

Security isn't just what we teach; it's how we operate...

Ransomware is one of the most dangerous threats...
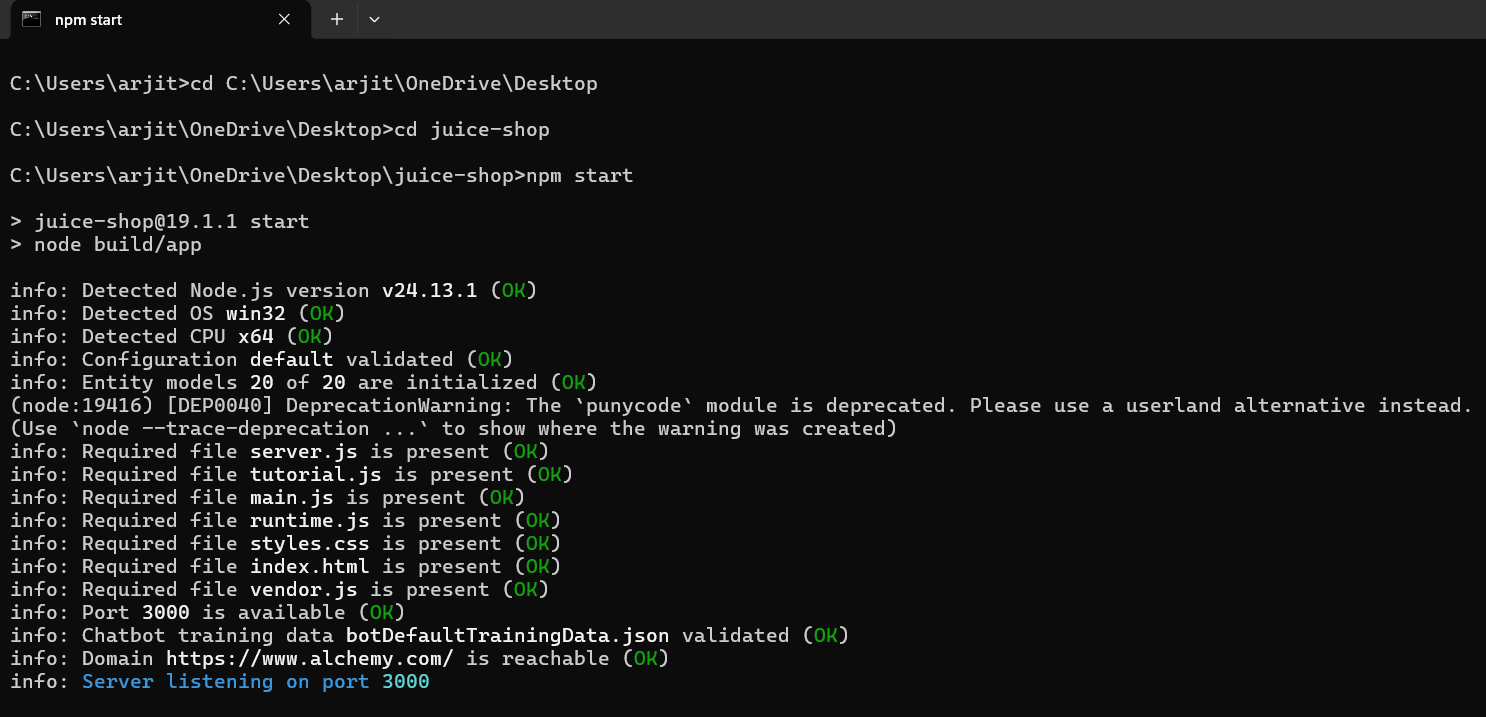
Web application vulnerabilities remain one of the biggest security risks for modern organizations. Attackers constantly look for weaknesses such as in...